AI vs. AI: When Artificial Intelligence Protects Our Company from Artificial Intelligence
The New Era of Cybersecurity: Machine Speed vs. Machine Speed
In 2026, cybersecurity is no longer human vs. human, but machine vs. machine. Cybercriminals leverage AI to automate and scale their attacks, while defenders deploy equally advanced AI systems to counter them. The digital battle is won by whoever wields the smarter AI.
The Stakes: $10.4 Billion
OutreachX projects that by 2027, AI-powered cybersecurity will save companies $10.4 billion. According to IBM, AI tools already save an average of $1.9 million per breach. But what happens if we fall behind in this arms race?
How AIs Fight Each Other
The “Bad AI” Arsenal
Cybercriminal AI is no longer science fiction, but an operational reality.
1. Emotet AI-Powered Malware
Emotet evolved from a simple banking Trojan into a self-modifying, AI-driven virus. It adapts its behavior in real time to evade traditional defenses.
2. Agentic AI Attacks
CrowdStrike’s 2025 Global Threat Report highlights how attackers increasingly deployed generative AI in 2024:
- Automated vulnerability scanning
- Tailored spear-phishing campaigns
- Supply chain compromises
- Deepfake-based social engineering
3. Machine-Speed Attacks
Breakout time—from initial attack to lateral spread—is now often under an hour. AI enables adversaries to:
- Write highly convincing phishing emails
- Generate fake websites and deepfake videos
- Inject malicious prompts and code
The “Good AI” Defense
Defensive AI doesn’t wait—it proactively hunts threats.
Google’s Big Sleep: The First AI-Powered Preemptive Defense
In July 2025, Google’s Big Sleep AI autonomously discovered and neutralized a zero-day vulnerability before anyone else even knew it existed.
This historic milestone proves:
- No human alerts needed—the AI runs autonomously
- High-risk issues are identified before they become known
- The vulnerability discovery model has been fundamentally reversed
Behavioral Analytics: The Heart of AI-Based Defense
Why Traditional Methods Fail
Traditional antivirus solutions rely on signature-based detection: they look for known patterns. But if attacking AI alters these patterns in real time, defenses fail instantly.
The problem:
- Signature-based methods are reactive
- They cannot recognize novel threats
- AI-powered malware consistently outsmarts them
Behavioral analytics and SOC in action
Modern SOC-driven security follows a different approach:
instead of focusing on individual tools or files, it concentrates on attack techniques and behavioral patterns.
- Behavior-based analytics: attackers constantly change their tools, but their methods remain consistent – recognizing these patterns is critical
- AI-supported 24/7 SOC monitoring: continuous oversight, proactive threat hunting, and rapid response through globally distributed operations
- Early ransomware detection: suspicious file activity, anomalous access patterns, and encryption behavior can be identified before real damage occurs
Machine Learning in Practice: Real Use Cases
- Predictive Analytics – AI predicts future threats from historical data. Example: Cylance analyzes millions of attributes to identify malicious patterns and stop attacks before they occur.
- Behavioral Anomaly Detection – Darktrace’s “Enterprise Immune System” learns a network’s normal behavior, then flags anomalies—even never-before-seen threats.
- False Positive Reduction – CrowdStrike Falcon uses AI to drastically reduce false alerts and improve accuracy.
The Future: Agentic AI and Autonomous Cybersecurity
What is Agentic AI?
Agentic AI systems make decisions and take actions autonomously.
Example: CrowdStrike Charlotte AI
- Validates whether an alert is a true threat
- Gathers and analyzes contextual data
- Implements adaptive, automated defenses
- Continuously learns from every incident
SOC-based hybrid defense: human expertise and AI together
AI is extremely fast, but interpreting complex business and technical context still requires human expertise.
That’s why modern SOC operations rely on a hybrid model:
- AI automates routine tasks and performs initial analysis
- SOC analysts handle complex incidents with real business impact
- the system continuously learns from human decisions
This approach ensures protection that is fast, accurate, and context-aware.
Practical Implementation for Enterprises
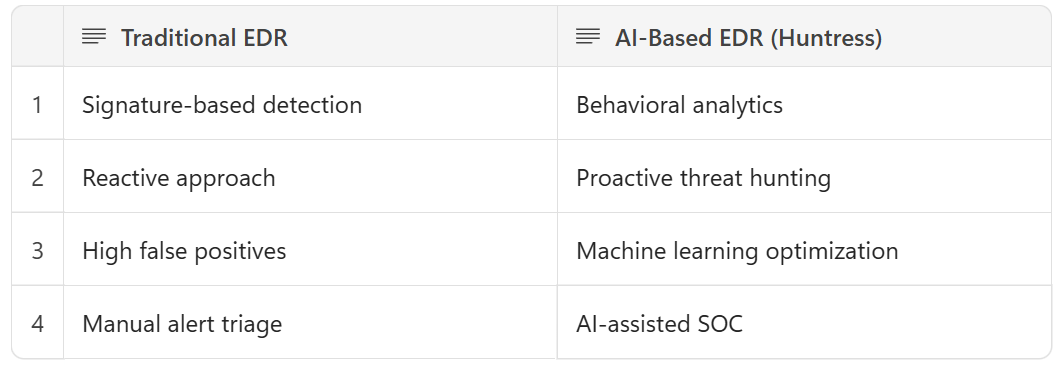
1. Modernizing EDR
2. Next-generation SIEM and automated incident response
In a modern SOC environment, the goal of SIEM solutions is not to generate more data, but to reduce noise and surface real threats.
SOC-driven response capabilities enable:
- rapid isolation of compromised endpoints
- automatic termination of malicious processes
- real-time threat intelligence integration into decision-making
This significantly reduces response times and limits the business impact of incidents.
Economic Impact of the AI War
- IBM: AI saves $2.2 million per incident
- Dwell time reduced—AI detects threats 60% faster
- Alert fatigue reduced 50% fewer false positives
The real value isn’t just a prettier dashboard—it’s compressed dwell time. When AI closes the loop from detection to containment in minutes, board-level metrics shift: fewer payouts, faster recovery, less revenue at risk.
Zero Trust and AI: The Perfect Match
Zero Trust assumes no entity is trustworthy by default—internal or external.
AI enhances this by enabling:
- Continuous verification in real time
- User and device behavior analysis
- Dynamic access restrictions
- Blocking the lateral movement of attacks
Challenges and Considerations
- Data Quality – AI models are only as good as the data fed to them. Garbage in, garbage out.
- AI Accountability – Who’s responsible when AI acts autonomously? Transparency and auditability are essential.
- Talent Gap – Skilled professionals must combine machine learning, cybersecurity fundamentals, and ethics/regulatory expertise.
The Road Ahead: 2026 and Beyond
Emerging Trends:
- Federated Learning – decentralized, privacy-friendly knowledge sharing
- Self-Healing Networks – AI detects, isolates, and remediates vulnerabilities automatically
- Quantum-Resistant AI – built for the era of quantum computing
Conclusion: Winning the AI War
The cybersecurity AI war is not future tense—it’s already happening daily. The question isn’t whether to use AI, but what kind of AI to use.
Keys to Success
- Prioritize behavioral analytics
- Embrace human–AI collaboration
- Continuously refine AI models
- Focus on proactive defense
In the AI war, the winners combine human insight with machine intelligence. Huntress does exactly that.
Ready to strengthen your defense against AI-driven attackers? Gloster Cloud experts help deploy Huntress AI-powered managed security and 24/7 SOC services.




